Understanding Crypto Hacks: 5 Notable Cases Uncovered
Five major cryptocurrency hacks have reshaped the industry’s security practices. The Mt. Gox disaster of 2014 lost $450 million through poor security protocols. In 2021, Poly Network suffered a $611 million theft with funds later returned. North Korea’s Lazarus Group stole $625 million from Ronin Network in 2022. The Wormhole Protocol lost $320 million to smart contract vulnerabilities. Binance experienced a $570 million cross-chain bridge hack. These cases illuminate the evolving nature of blockchain security threats.
Key Takeaways
- Mt. Gox lost 850,000 Bitcoins in 2014 due to poor security practices and improperly stored private keys.
- The 2021 Poly Network hack stole $611 million across multiple blockchains but ended with complete fund return.
- Ronin Network suffered a $625 million theft when hackers compromised validator nodes through social engineering.
- Wormhole Protocol lost $320 million when attackers exploited smart contract verification flaws to mint unauthorized tokens.
- Binance’s BNB chain lost $570 million when hackers bypassed bridge verification processes to create new tokens.
The Mt. Gox Catastrophe: Lessons From the First Major Exchange Hack

When cryptocurrency was still finding its footing in the early 2010s, Mt. Gox emerged as a pioneer, handling over 70% of all Bitcoin transactions by 2013. Founded by Jed McCaleb and later acquired by Mark Karpelés, the exchange quickly became the industry’s centerpiece.
However, poor security practices led to its downfall. Hackers exploited vulnerabilities in Mt. Gox’s system, gradually stealing approximately 850,000 Bitcoins (valued at $450 million) over several years. Unencrypted private keys and excessive use of hot wallets made the theft possible.
The February 2014 collapse and subsequent bankruptcy filing sent shockwaves through the industry, prompting increased regulatory scrutiny and distrust in cryptocurrencies.
This catastrophe ultimately spurred critical improvements in exchange security practices, including cold storage implementation and multi-signature wallets. Furthermore, it highlighted the importance of strong passwords and enhanced security measures for safeguarding digital assets.
Poly Network’s $611 Million Breach and the Unexpected Return

The August 2021 Poly Network hack stands as one of cryptocurrency’s most remarkable security incidents, not only for its unprecedented $611 million theft but also for its surprising resolution.
Attackers exploited vulnerabilities in smart contract systems across Ethereum, Binance Smart Chain, and Polygon blockchains, specifically targeting EthCrossChainManager contracts.
What distinguishes this case was the hacker’s decision to return all stolen funds within 15 days.
Poly Network dubbed the attacker “Mr. White Hat,” even offering a $500,000 bounty and a security advisor position.
Tether froze $33 million in stolen USDT, limiting laundering options.
The incident highlighted both DeFi security vulnerabilities and blockchain transparency’s effectiveness in tracking stolen assets, ultimately prompting enhanced security measures throughout the industry. Additionally, this case underscores the importance of secure wallets in protecting crypto assets from potential hacks.
Ronin Network: How North Korean Hackers Stole $625 Million

March 2022 marked another watershed moment in cryptocurrency security history as the Ronin Network suffered a catastrophic breach, eclipsing even the massive Poly Network hack in financial scale. The Lazarus Group, a North Korean state-sponsored cybercrime organization, compromised five of nine validator nodes on Sky Mavis’s Ronin bridge, enabling them to approve fraudulent transactions.
| Attack Element | Details |
|---|---|
| Stolen Assets | 173,600 ETH + $25.5M USDC |
| Method | Social engineering + validator compromise |
| Detection | Delayed (6 days after occurrence) |
| Attribution | North Korea’s Lazarus Group |
| Recovery | Approximately $30M recovered |
The hackers employed sophisticated laundering techniques, including DEX swaps, Tornado Cash mixing, chain hopping, and cryptocurrency conversions. This breach highlighted critical vulnerabilities in cross-chain bridges and prompted industry-wide security reassessments. Implementing strong multi-factor authentication practices could have potentially mitigated the risk of such an attack.
Smart Contract Vulnerabilities: The Wormhole Protocol Exploit
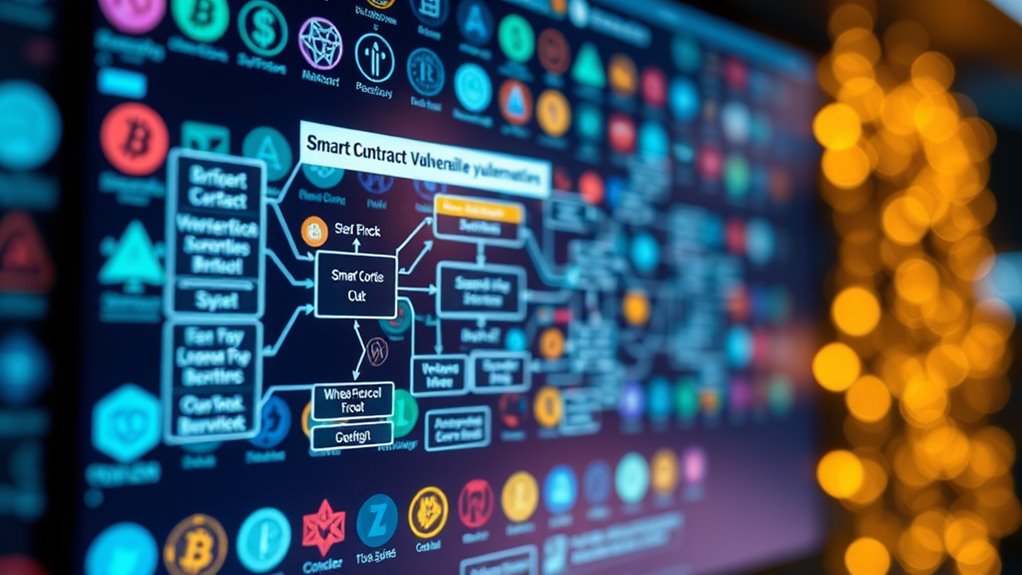
February 2022 witnessed one of cryptocurrency’s most significant security breaches when hackers exploited critical vulnerabilities in the Wormhole Protocol’s smart contract architecture, resulting in a staggering $320 million theft.
The attack targeted verification flaws on Solana, where the perpetrator injected a counterfeit Sysvar account to bypass security checks. This manipulation enabled the creation of fraudulent messages requesting 120,000 wETH tokens.
After minting these tokens, the attacker quickly bridged 90,000 ETH to the Ethereum blockchain.
Wormhole’s response included temporarily suspending operations and offering a $10 million bounty for exploit information.
The incident highlighted fundamental vulnerabilities: signature verification failures, missing address validation, and the use of deprecated functions.
This case demonstrated that cross-chain bridges, despite their utility, can present significant security challenges without proper verification mechanisms. Furthermore, employing rigorous testing and auditing can significantly reduce vulnerabilities in smart contracts.
Cross-Chain Bridge Attacks: Analyzing the Binance BNB Hack

In October 2022, cryptocurrency markets faced another significant security breach when attackers compromised Binance’s BSC Token Hub, resulting in the theft of approximately 2 million BNB tokens valued at $570 million.
The attackers exploited a vulnerability in the bridge’s verification process, specifically in the Merkle tree verification mechanism. By forging proof messages, they minted new BNB tokens without proper authorization.
Binance responded swiftly by halting the Binance Smart Chain and freezing some funds, limiting potential losses.
Following the attack, the price of BNB dropped by 3.5% as investor confidence wavered. The incident highlighted the persistent vulnerability of cross-chain bridges, which connect different blockchains but often become prime targets for hackers.
Binance later proposed governance votes and a bug bounty program to strengthen security measures. As regulatory frameworks evolve, they will likely address consumer protection to mitigate risks associated with such attacks in the future.
Frequently Asked Questions
How Are Stolen Cryptocurrencies Typically Laundered?
Stolen cryptocurrencies are typically laundered through mixing services, chain hopping, smurfing, crypto ATMs, and privacy coins. Launderers also utilize decentralized exchanges, OTC brokers, non-compliant exchanges, gambling platforms, and peer-to-peer networks.
Can Victims Recover Insurance for Crypto Hacks?
Victims can claim insurance for crypto hacks, but recovery often depends on policy specifics, type of hack, and exchange coverage limitations. Most policies exclude individual account breaches, making extensive coverage rare.
What Role Do Bug Bounty Programs Play in Preventing Hacks?
Bug bounty programs incentivize ethical hackers to discover vulnerabilities before malicious actors exploit them. They provide continuous security testing, identify zero-day vulnerabilities, and demonstrate an organization’s commitment to proactive cybersecurity measures.
How Do Regulatory Responses Differ Globally After Major Hacks?
Regulatory responses to major crypto hacks vary greatly across regions. While some nations implement extensive frameworks like EU’s MiCA, others focus on mandatory registration or stringent KYC requirements. Some jurisdictions resort to outright bans.
What Technological Innovations Emerged Specifically to Counter These Vulnerabilities?
Technological innovations addressing cryptocurrency vulnerabilities include hardware cold wallets, advanced encryption protocols, biometric authentication, AI-powered fraud detection systems, and improved blockchain architecture with enhanced security features like multi-signature verification and decentralized identity solutions.
Conclusion
Cryptocurrency hacks continue to evolve as security measures advance. Since 2011, over $14 billion in crypto assets have been stolen through various exploits—enough to purchase approximately 28,000 average American homes. Understanding these vulnerabilities remains essential for investors and developers alike, as blockchain technology grows more interconnected. While security protocols improve, the decentralized nature of cryptocurrency presents ongoing challenges that require vigilance from all participants in the ecosystem.