
Cold Storage Vs Hot Storage: What’s Best for Your Crypto?
Cold storage keeps cryptocurrency keys completely offline, providing maximum security for long-term holdings but sacrificing convenience. Hot wallets remain connected to the internet, offering easy access for frequent trading at the cost of increased vulnerability to hacking. Most investors benefit from a hybrid approach—storing small amounts for daily transactions in hot wallets while securing larger holdings in cold storage. The right balance depends on individual trading frequency, risk tolerance, and portfolio size. The following sections explore implementation strategies for ideal protection.
Key Takeaways
- Cold storage keeps keys offline with enhanced security, making it ideal for long-term holdings and larger crypto assets.
- Hot storage offers constant internet connectivity and convenient access, facilitating easier day-to-day transactions for active traders.
- Your choice should depend on portfolio size, risk tolerance, and usage patterns—many users implement a dual strategy.
- Cold storage minimizes network exposure but requires managing seed phrases, while hot wallets trade security for convenience.
- Consider a hybrid approach: use hot wallets for frequent transactions and cold storage for long-term investments exceeding your risk threshold.
Understanding Cold and Hot Storage Fundamentals

While the cryptocurrency market continues to evolve, the fundamental distinction between cold and hot storage remains critical for investors seeking to protect their digital assets.
These methods differ primarily in their connection to the internet, which greatly impacts their security profile.
Cold storage keeps private keys completely offline, making them less vulnerable to hacking attempts. Users maintain full control of their keys, signing transactions offline before broadcasting them through connected devices.
In contrast, hot storage maintains constant internet connectivity, offering convenience for frequent trading but potentially compromising security.
Both storage types utilize public and private keys for transactions, but they serve different purposes.
Cold storage, with its offline nature and enhanced security measures like PINs and biometric authentication, is ideal for long-term holdings, while hot wallets facilitate easier day-to-day transactions. Implementing practices such as using hardware wallets can further enhance the security of your cold storage solutions.
Security Considerations When Choosing Storage Methods

The fundamental decision between cold and hot storage ultimately hinges on security considerations that every cryptocurrency holder must evaluate. Each storage method presents distinct security profiles that align with different user needs and risk tolerances.
| Security Factor | Cold Storage | Hot Storage |
|---|---|---|
| Network Exposure | Offline, minimal attack surface | Always online, larger attack surface |
| Physical Risk | Requires physical protection | Less dependent on physical security |
| Key Management | Self-custody with offline keys | Often managed by third parties |
| Recovery Options | Seed phrases and backups | Platform-dependent recovery methods |
When selecting a storage solution, users should assess their technical expertise, frequency of transactions, and asset value. Cold storage offers superior security for long-term holdings, while hot wallets provide convenience for active trading, albeit with increased vulnerability to online threats. Additionally, employing secure wallets is crucial to ensure the safety of your digital assets.
The Trade-Off Between Convenience and Protection

Choosing between convenience and security represents the fundamental dilemma cryptocurrency users face when selecting storage solutions.
Hot wallets offer immediate access and user-friendly interfaces that simplify daily transactions, but this accessibility comes with increased vulnerability to online threats.
Cold storage provides robust protection by keeping private keys offline, though it requires additional steps to access funds and often involves purchasing hardware devices.
A user’s decision typically depends on their risk tolerance and usage patterns.
Frequent traders benefit from hot wallets‘ immediate accessibility during market fluctuations, while long-term investors may prioritize the enhanced security of cold storage.
Many experienced cryptocurrency users employ both methods strategically—keeping small amounts for regular transactions in hot wallets while securing larger holdings in cold storage, effectively balancing convenience with protection. Additionally, users can maximize security by following best practices, such as avoiding third-party software and regularly checking for firmware updates on their hardware wallets.
When to Use Cold Storage for Maximum Security

Cold storage provides essential protection for investors holding large amounts of cryptocurrency, with major exchanges like Binance securing over 250,000 BTC in this manner.
The offline nature of cold wallets shields sensitive information like private keys from unauthorized access and potential cyber threats.
Statistics showing that approximately 20% of all crypto coins have been lost due to theft and technical failures further emphasize the importance of cold storage for safeguarding valuable digital assets. Implementing trusted key management systems is crucial for enhancing the security of your private keys even in cold storage solutions.
Large Holdings Protection
Significant cryptocurrency investments demand robust security measures that match their value. For substantial holdings, cold storage methods like hardware wallets, paper wallets, and air-gapped systems provide essential protection against online threats and exchange vulnerabilities.
Cold storage solutions offer enhanced security benefits, including protection from hacking attempts, phishing scams, and exchange breaches. They also provide complete control over private keys, reducing dependency on third parties. Additionally, securely storing your seed phrase is critical to maintaining the integrity of your cold storage setup.
Many businesses and serious investors implement multi-signature wallets, requiring multiple approvals for transactions and creating additional security layers.
While cold storage introduces some inconvenience and requires careful management of recovery phrases, these trade-offs are generally justified when protecting large investments.
The initial cost of hardware wallets and technical setup becomes negligible compared to the security benefits for valuable crypto portfolios.
Sensitive Information Safeguarding
Beyond protecting large holdings, the safeguarding of sensitive information represents a primary concern for cryptocurrency owners. Cold storage methods provide extensive protection against various forms of digital threats by isolating private keys and authentication data from online exposure.
- Private key isolation – Cold wallets keep encryption keys completely offline, preventing remote access attempts.
- Phishing resistance – Without internet connection, users cannot accidentally submit credentials to fraudulent websites.
- Protection during transactions – Offline signing capabilities allow verification without exposing sensitive data.
- Recovery phrase security – Physical storage of backup phrases reduces the risk of digital compromise.
These security measures are particularly essential for individuals who prioritize privacy and confidentiality, especially when handling financial information that could be targeted by sophisticated attackers familiar with cryptocurrency vulnerabilities. Additionally, implementing multi-factor authentication alongside cold storage enhances security by requiring multiple verification methods to access sensitive data.
Hot Wallets: Balancing Accessibility and Risk

Hot wallets represent the frontline of cryptocurrency storage solutions, offering users immediate access to their digital assets through internet-connected platforms. These wallets, including software options like MetaMask and Exodus, provide convenience through quick transactions and user-friendly interfaces across multiple devices.
Despite their accessibility advantages, hot wallets carry inherent security risks due to their constant internet connectivity. They remain vulnerable to hacking attempts, phishing scams, and malware attacks that could compromise private keys. Recent exchange breaches underscore these vulnerabilities.
Users can mitigate risks by implementing two-factor authentication, keeping software updated, and storing only small amounts needed for daily transactions. Additionally, employing multi-factor authentication can significantly enhance the overall security of hot wallets.
Balancing the trade-off between convenience and security requires regular monitoring, maintaining offline backups, and staying educated about emerging threats.
Hybrid Storage Strategies for Different Portfolio Sizes

Hybrid strategies that combine both hot and cold storage can be tailored to match portfolio requirements, balancing security with convenience based on asset value and usage patterns.
- Small portfolios may use hot wallets for frequently accessed funds while securing long-term holdings in cold storage, despite higher initial hardware costs.
- Medium portfolios benefit from a balanced approach, keeping trading funds accessible while protecting larger holdings.
- Large portfolios prioritize cold storage for significant holdings, using hot wallets only for active trading portions.
- All portfolio sizes should implement proper backup practices for private keys, regardless of the storage method chosen. Additionally, understanding the differences between hot and cold wallets can help investors make informed decisions about their storage strategies.
This approach offers flexibility while maintaining appropriate security measures across different investment levels.
Common Vulnerabilities and How to Mitigate Them
Security vulnerabilities exist across all cryptocurrency storage methods, posing considerable risks to investor assets regardless of portfolio size.
Hot wallets face threats from network exposure, phishing attacks, and malware, while cold storage solutions remain vulnerable to physical theft and seed phrase loss.
For hot wallets, implementing two-factor authentication, regular software updates, and strong password practices considerably reduces risk. Users should limit funds stored in these internet-connected wallets and monitor transactions regularly.
Cold storage users must prioritize seed phrase security, using physical protection like fire-safe boxes and keeping firmware updated.
Multi-signature wallets provide an additional security layer against unauthorized access.
Advanced technologies like Multi-Party Computation (MPC) and hardware-based verification are increasingly available to enhance protection across both storage types, with quantum-resistant cryptography emerging as essential for long-term security. Additionally, utilizing a VPN for crypto security can further safeguard transactions and protect against potential cyber threats.
Recovery Options for Both Storage Types
Recovery of cryptocurrency investments requires planning for both storage methods, with properly secured seed phrases being essential for wallet restoration.
Many exchanges now offer streamlined recovery processes for users who lose access to their accounts, though these solutions often involve identity verification.
Regardless of storage type, maintaining secure, redundant backups of critical recovery information provides the best chance of regaining access to digital assets after a loss.
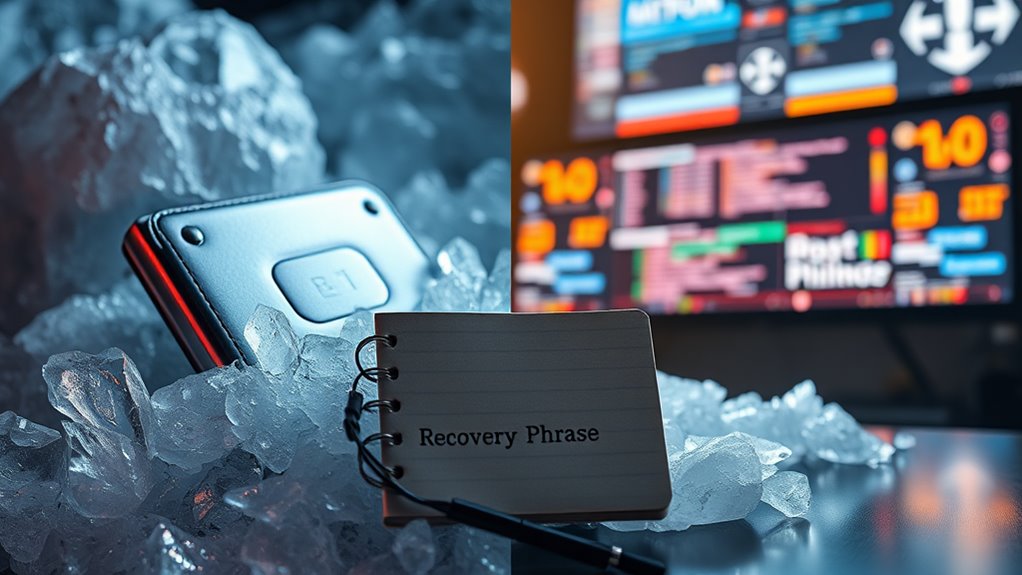
Backup Seed Phrases
Safeguarding seed phrases stands as perhaps the most critical aspect of cryptocurrency ownership, regardless of whether one uses cold or hot storage solutions.
These phrases, typically following the BIP39 standard, contain all necessary information to recover funds on the blockchain.
For effective seed phrase management:
- Choose durable physical storage methods like pencil on paper or metal engraving for longevity.
- Consider splitting assets between cold and hot wallets to balance security with accessibility.
- Explore enhanced security options such as multisignature wallets or two-factor seed phrases.
- Never store seed phrases digitally where they might be vulnerable to hacking.
Both cold storage hardware wallets and internet-connected hot wallets rely on proper seed phrase protection, making secure storage methods essential for preventing theft and ensuring recovery capabilities. Additionally, understanding the differences between cold and hot storage can help you make more informed decisions about managing your cryptocurrency assets.
Exchange-Based Recovery Solutions
Recoverability presents an essential dimension of cryptocurrency security that transcends the choice between hot and cold storage solutions. Major exchanges now offer specialized recovery services for both storage types, often collaborating with law enforcement agencies to trace stolen assets.
For cold storage issues like damaged hardware wallets, companies such as KeychainX provide repair services for devices like Trezor and Ledger.
Hot wallet recovery typically involves addressing security breaches through blockchain analysis and digital forensics.
Recovery professionals employ various technical approaches, including wallet encryption cracking, corrupted file repair, and private key restoration.
The effectiveness of these recovery efforts often depends on immediate action following asset loss, cooperation with authorities, and engagement with reputable recovery firms that utilize blockchain forensics and advanced cryptography to track and secure compromised funds.
Best Practices for Managing Your Crypto Assets

Several critical strategies exist for effectively managing cryptocurrency assets in today’s volatile digital market. Implementing proper risk management techniques while maintaining appropriate security measures can markedly protect investments from market fluctuations and security threats.
Effective cryptocurrency management requires balancing robust security protocols with strategic risk assessment in today’s unpredictable digital landscape.
- Diversify across multiple exchanges to reduce dependency on a single platform and minimize exposure to exchange-specific risks.
- Implement a hybrid storage approach by keeping actively traded assets in hot wallets while storing long-term holdings in cold storage.
- Set strict risk thresholds including stop-loss orders and limiting exchange holdings to a predetermined percentage of total assets.
- Establish verification protocols for counterparties by researching their reputation, understanding their security policies, and evaluating their insurance coverage.
Regular monitoring of market conditions and maintaining updated security practices further enhance protection of digital assets.
Frequently Asked Questions
How Much Does a Hardware Wallet Typically Cost?
Hardware wallets typically cost between $50 and $250, with entry-level models like the Trezor Model One priced around $49, mid-range options at $79, and premium devices such as NGRAVE ZERO reaching approximately €498.
Can I Stake My Cryptocurrency While It’s in Cold Storage?
Frozen wallets, active earnings: Yes, cryptocurrency staking is possible from cold storage. This process, called cold staking, allows investors to earn rewards while keeping private keys offline, utilizing specialized hardware wallets and delegation mechanisms.
Are There Insurance Options for Crypto Stored in Hot Wallets?
Yes, insurance options exist for cryptocurrencies stored in hot wallets. Several providers offer policies covering theft and hacking risks, though coverage limits and costs vary based on asset types and security measures implemented.
How Often Should I Update My Wallet Software?
Like vigilant sentinels guarding treasure, wallet software requires consistent attention. Hot wallets should be updated immediately when available, while cold storage typically needs firmware updates every 6-8 months or when security patches are released.
What Happens to My Crypto if the Wallet Company Goes Bankrupt?
If a custodial wallet provider declares bankruptcy, users’ crypto may become part of the bankruptcy estate. Customers typically become unsecured creditors with limited recovery prospects and face potential withdrawal restrictions during proceedings. Non-custodial wallets eliminate this risk.
Conclusion
In the cryptocurrency ocean, your choice of storage represents the anchor of your financial security. Like a fortress versus a revolving door, cold and hot storage solutions each serve distinct purposes in the crypto ecosystem. By balancing security needs with accessibility requirements, investors can navigate the digital asset landscape with confidence. Ultimately, the most secure approach combines both methods, tailored to individual risk tolerance and portfolio value.














